Lab 1.4 – IPv4 Packet Analysis
This lab focused on examining network traffic at the IPv4 layer, with an emphasis on identifying abnormal or suspicious behavior within the packet capture.
Lab Setup
For this exercise, I used the capture file called ipv4.pcap.
Once downloaded, I opened the file in Wireshark and began my analysis.
Exercise 1 – Analyzing the First IPv4 Packet
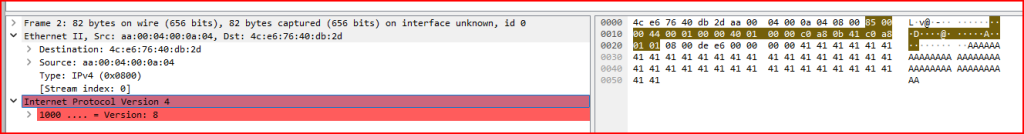
a) What version of IP is the first packet?
We can find this either by looking at the Ethernet header or the IP header. Looking at the IP Header, the IP version is located in the higher-order nibble of the 0 byte offset. We can see there that this is an IPv4 packet.
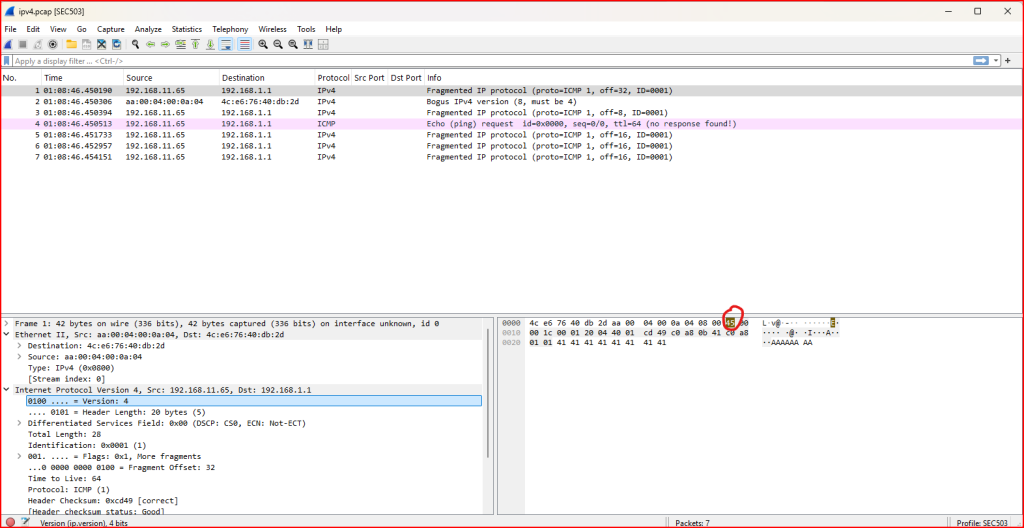
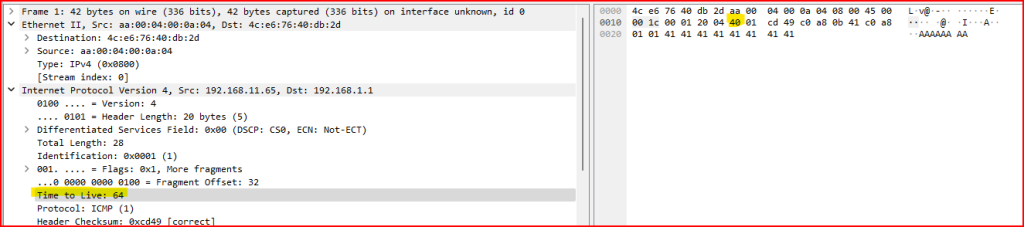
b) What is the IP Time To Live value, in decimal, in this packet?
To answer this, I examined the IPv4 header of the first packet in the ipv4.pcap file. I specifically looked at the Time To Live (TTL) field, which determines how many hops (routers) the packet can pass through before being discarded.
The TTL field is located 8 bytes into the IP header, but Wireshark conveniently displays this value directly in the decoded packet details. In this case, the TTL value was 64, which is a common default for Linux-based systems.
This value can also give clues about the operating system or network behavior based on how far the packet has traveled.
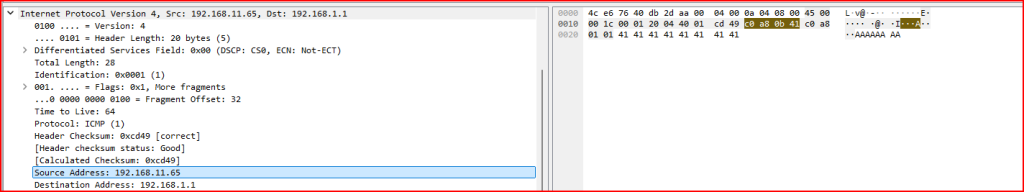
c) What is the source IP address, in hexadecimal, in the first packet?
To find the source IP address in hexadecimal, I examined the IPv4 header in the first packet of the ipv4.pcap capture. The source IP address is located between bytes 12 and 15 from the start of the IP header.
Wireshark makes this easy by displaying both the decimal and hexadecimal representations. For the first packet, the source IP is 192.168.11.65 in decimal, which corresponds to 0xc0 0xa8 0x0b 0x41 in hexadecimal.
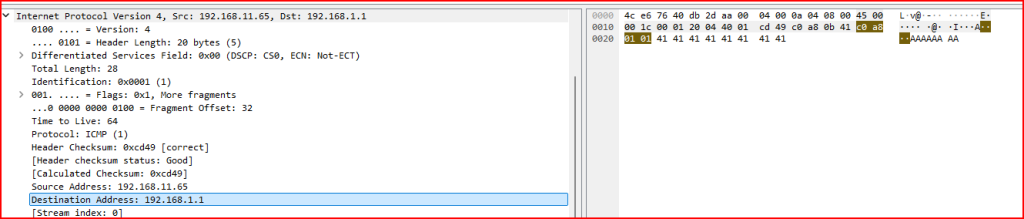
d) What is the destination IP address, in hexadecimal, in the first packet?
To find the destination IP address in hexadecimal, I examined the IPv4 header of the first packet in the ipv4.pcap file. According to the IP header structure, the destination IP is stored between bytes 16 and 19 from the start of the IP header.
Wireshark clearly shows this value in both hexadecimal and decimal. In this case, the destination IP is 192.168.1.1, which corresponds to the hexadecimal representation 0xc0 0xa8 0x01 0x01.
Exercise 2 – Identifying Abnormalities in the IPv4 Header
In this exercise, I examined the second packet in the ipv4.pcap capture and identified two key problems with its IP header.
Problem 1: Invalid IP Version
The first issue is that the IP header lists version 8, which is not a valid or supported IP version. Only versions 4 and 6 are in use today. Because of this, Wireshark marks the packet in red and does not attempt to decode it further.
Problem 2: Invalid Header Checksum
After inspecting the raw packet bytes, I found another issue in bytes 10 and 11, which represent the IP header checksum. The value was 0x0000, which is invalid and indicates the packet may have been corrupted or crafted improperly.
Impact
Both of these abnormalities would cause the packet to be dropped immediately by the first router or system it attempts to pass through. This exercise helped me understand how malformed packets are detected and discarded at the network layer.
Exercise 3 – Hex Analysis Using tcpdump
In this part of the lab, I used the tcpdump command-line tool to inspect raw packet data and answer questions related to the third packet in the ipv4.pcap capture.
To extract the first few packets in hexadecimal format, I ran:
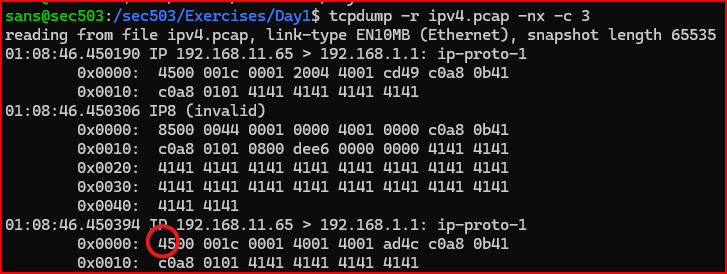
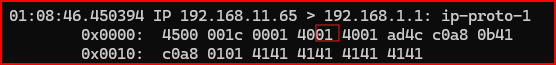
a) What version of IP is this packet? What is the header length if the packet ?
By looking at the raw hexadecimal output of the third packet, I found it starts with the byte 0x45. This first byte breaks down into two nibbles:
- 4 → IP version
- 5 → header length
So, the version number of this packet is IPv4, as indicated by the high-order nibble of the first byte.
The header length field is in units of double word so it has to be multiplied by 4 to be converted to a length of 20 bytes.
b) What is the embedded protocol in this packet, according to the IP header?
To determine the embedded protocol, I examined byte offset 9 in the IP header of the third packet. This byte indicates which protocol is encapsulated within the IPv4 packet.
Using the tcpdump output, I located the value at this offset. For this packet, the value was 0x01, which corresponds to ICMP (Internet Control Message Protocol).
Exercise 4 – Calculating ICMP Header and Data Length
In this task, I analyzed the fourth packet in the ipv4.pcap file to determine how many bytes were used by the ICMP header and data, following the IPv4 header.
To do this, I used two values from the IP header:
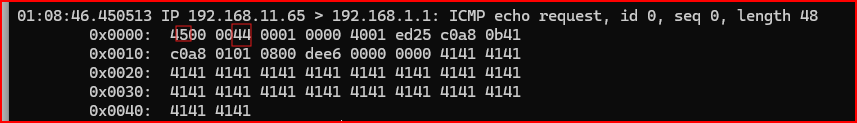
- Total Length: 68 bytes (it is found in the 3rd byte offset of the IP Header // it has a hexadecimal value of 0x44)
- Header Length: 20 bytes (which is shown as a value of
5in the header, multiplied by 4)
By subtracting the IP header length from the total IP datagram size:68 - 20 = 48 bytes
So, the ICMP header and data together occupy 48 bytes in this packet.
Leave a Reply